Loading...
Loading...

A global payments firm processing 1,000+ alerts per day stopped hiring SOC analysts last year. So did a Fortune 500 utility with $20B in revenue and 21,000 employees. Both deployed an AI SOC agent and hit 100% alert coverage with the same team, the same stack, in 30 minutes.
An AI SOC uses autonomous agents to triage, investigate, and respond to security alerts without human intervention on each alert. Instead of scaling analyst headcount to match alert volume, an AI SOC agent absorbs the investigative workload — typically resolving 90–95% of alerts automatically — so your existing security operations center team covers 100% of threats without adding staff.
I’ve had variations of this conversation with dozens of SOC leaders in the past six months. The question is always the same: how do we cover more without hiring more? The answer isn’t a better recruiting strategy. It’s recognizing that headcount was never the right variable.
SOC alert volume grows exponentially — 1,968 cyberattacks per week in 2025, up 70% since 2023 (Checkpoint Research). Analyst supply grows linearly at 9% per year against 18% demand growth. The global cybersecurity workforce gap stands at 4.8 million (ISC2 2025 Workforce Study), and the average SOC analyst position takes seven months to fill. The math doesn’t converge.
Fifteen percent of organizations report it takes two years or longer to fill a single SOC role. And ironically, the average tenure of the person you hire is 14 months. Meanwhile, mean time to respond stretches as alert queues grow faster than any incident response team can clear them.
Every security operations center is already rationing coverage. When 40% of alerts go uninvestigated and your team doesn’t know which 40%, the strategy isn’t “hire faster.” The strategy is structurally broken.
The curves diverged years ago. Hiring was never going to converge with alert volume.
The global payments firm runs 1,000+ alerts per day through a SOC team that hasn’t grown in over a year. Simbian’s AI SOC Agent handles alert triage, autonomous investigation, and incident response — 92% of alerts resolved in production without human intervention. The remaining 8% get full SOC analyst attention. Not triaging. Investigating.
The Fortune 500 industrial tells the same story at a different scale. $20B revenue. 21,000 employees. Same SOC team. 100% coverage. Deployed in 30 minutes.
In both cases, deployment didn’t require playbooks, professional services engagements, or months of tuning. The agent connects via API to existing tools — SIEM, EDR, XDR, identity, network — and starts resolving alerts immediately. Zero playbooks. No endpoint agents.
What changed wasn’t the team. It was the throughput.
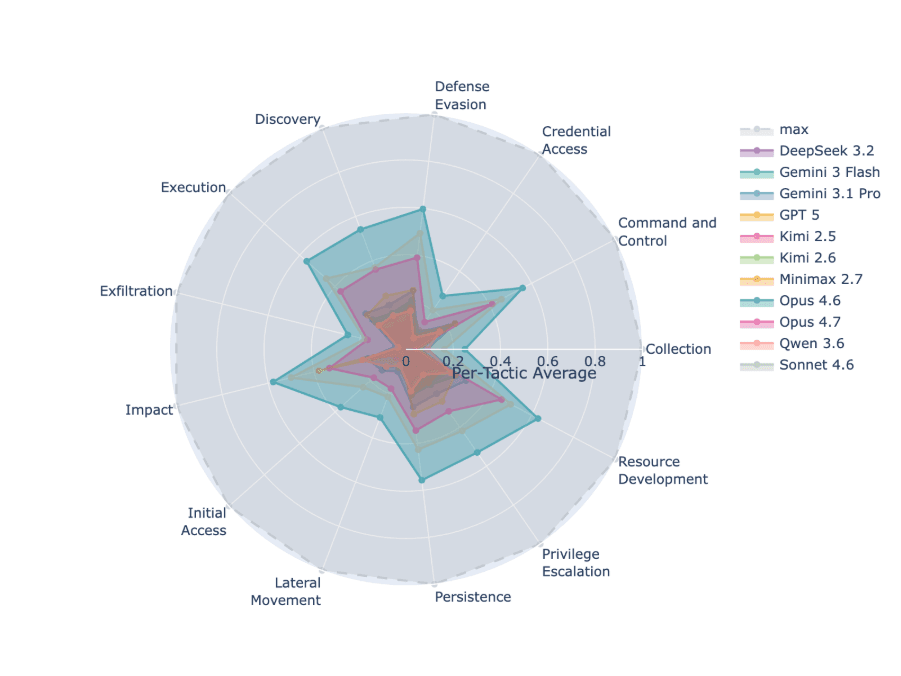
Most AI SOC platforms wrap raw large language models in an interface without the surrounding intelligence needed for real-world threat detection and autonomous investigation. Simbian’s Cyber Defense Benchmark proves this with reproducible data. In an open evaluation of eleven leading frontier LLMs on real-world cyber defense tasks across 105 attacks and close 900 runs Zero models passed.
The best model on its best tactic scored a D- at 63%, and averaged 43%. As a group, LLM averaged 18%, while most models scored less than 10% on some critical tactics. That’s frontier AI, unassisted, on actual defensive scenarios involving real attacker movement through real systems. Not promising. Failed.
Most vendors pitching “AI SOC” are wrapping raw LLMs in an interface and calling it autonomous. The benchmark exposes the gap between marketing and production.
Four questions cut through the noise:
Does it reason or follow rules? If the answer involves playbooks, it’s SOAR with a chatbot.
Can it handle novel threats? Correlation engines break on zero-days. Reasoning engines adapt.
What’s the benchmark? Ask for reproducible data. If the answer is “trust us,” walk.
Does it work on day one? Months of playbook engineering means the value is professional services, not AI.
“There’s intense focus on how AI can be used for cyberattacks. What we wanted to answer is whether today’s AI can actually defend by finding attackers as they move through real systems. Based on reproducible, real-world data, the answer is no. The LLMs must be accompanied with outside intelligence in the form of a sophisticated harness or intelligent software. Simbian has been able to get 95% accuracy in production enterprise environments on cyber defense SecOps following some of these techniques.”
— Ambuj Kumar, Founder & CEO, Simbian
Raw LLMs averaged 18%. Simbian’s production harness: 95%. The harness — not the model — is the whole story.
The capacity story extends beyond alert resolution and the SOC queue. Simbian’s AI Threat Hunt Agent generates and validates hypotheses autonomously — the proactive work most teams never reach because they’re buried in alerts. The AI Pentest Agent runs continuous offensive testing from the same platform, exposing weaknesses before attackers find them.
One platform. Three functions your SOC team would struggle to staff even if the budget existed.
This is what capacity means when you change the equation. Not faster triage. Not better dashboards. Structural expansion — from reactive alert processing to full-spectrum security operations.
What This Means for SOC Leaders
If you run security for the enteprise: The question stops being “how many analysts do we have?” and becomes “what percentage of threats do we investigate?” When 92% of alerts resolve autonomously in production — including nights, weekends, and holidays — the conversation shifts from headcount requests to capability posture. That’s the defensible answer to “what’s our AI security posture?”
The budget math changes too. Instead of requesting three positions that take seven months each to fill, you deploy in 30 minutes and demonstrate 100% coverage in week one.
If you run the queue: The Tier-1 grind ends. Not gradually — structurally. Seventy-one percent of SOC workers rate their pain at 6-9 out of 10 (SANS/Devo 2022 SOC Performance Report, corroborated by ISC2’s 2025 findings). Fifty-five percent have considered walking away. The revolving door doesn’t close with wellness stipends. It closes when the work itself changes.
When alert processing becomes investigation engineering and context curation, the career path stops being “survive two years of Tier-1 and hope for a promotion.” It becomes security engineering from day one. Analysts stay. They grow. And the SOC gets smarter.
Q: How do you scale a SOC without adding headcount? A: Deploy an AI SOC agent that autonomously triages, investigates, and responds to alerts across your existing stack. Simbian resolves 92% of alerts in production without human intervention — your team covers the remaining 8% that requires human judgment, at full depth.
Q: What’s the difference between AI SOC and SOAR? A: SOAR executes static playbooks that break on novel threats and require constant maintenance engineering. An AI SOC agent reasons from security alerts and context — no playbooks, no correlation rules. SOAR’s ceiling is roughly 25% automation. Simbian’s production floor is 92%.
Q: Can AI replace SOC analysts? A: No, and it shouldn’t. Simbian augments your team — handling the high-volume investigative workload so analysts focus on the 8% that requires human expertise, strategic threat hunting, and security engineering. The role evolves. The team doesn’t shrink.
Q: How do you evaluate AI SOC vendors without getting agent-washed? A: Four questions: Does it reason or follow rules? Can it handle threats it hasn’t seen before? What reproducible benchmark data exists? Does it deliver value on day one without months of tuning? The AI SOC Buyer’s Scorecard provides a structured framework for this evaluation.
Q: How quickly does an AI SOC agent deploy? A: Simbian deploys in 30 minutes via API-level integrations. No PowerShell, no endpoint agents, zero playbooks to write. First alerts resolve immediately. Production readiness in under four weeks.
![]()
Download the AI SOC Buyer’s Scorecard — a structured framework for evaluating any AI SOC solution. Then read the Cyber Defense Benchmark — the reproducible data behind the claims in this post.
Join the conversation live — April 29 webinar: Claude and OpenAI Will Change Security. Just Not the Way You Think.
Or skip straight to the proof: book a 15-minute walkthrough on your SIEM.