Loading...
Loading...
Recent announcements from AI companies such as Anthropic around application security tooling, for example Claude Code security capabilities, highlight how foundation model providers are raising the bar in the AppSec space. While these developments are notable, they represent a limited value proposition for security teams compared to the AI SecOps platform offered by Simbian AI.
Anthropic and OpenAI operate at the foundation model layer. Their application security efforts largely focus on improving how developers analyze or generate secure code.
This naturally leads to developer-centric tools, such as static code analysis, code vulnerability detection, secure code generation, and code review assistance. These tools are useful but represent only a small slice of security operations. In most organizations, AppSec is only one component within a much larger operational security environment that includes infrastructure monitoring, identity and access controls, network exposure analysis, incident response, threat detection, compliance, and reporting.
Simbian focuses on this broader operational layer, which holistically meets the needs of security teams.
One of the biggest differences between AppSec tools and real SecOps is context.
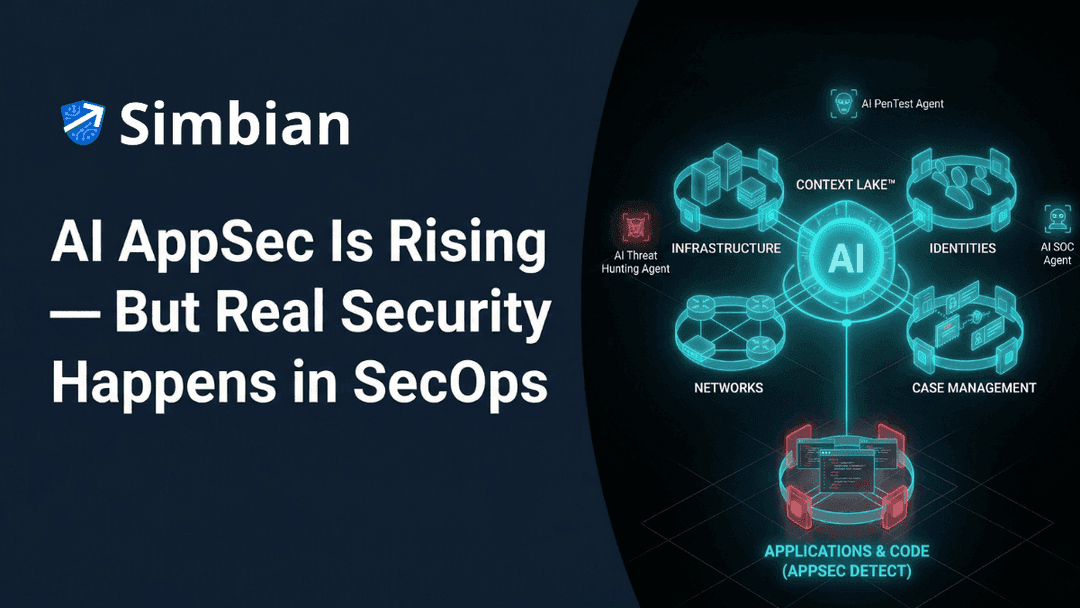
Simbian uses a Context Lake™, which aggregates and correlates signals from across the entire organizational environment — applications, infrastructure, networks, identities, and operational workflows.
This context fundamentally changes how vulnerabilities are evaluated.
For example, a critical vulnerability inside an isolated sandbox environment may represent minimal risk, while a moderate vulnerability on a host that could be used as a jump point to internal infrastructure could represent a serious exposure.
Traditional AppSec tools often flag issues without environmental awareness, resulting in security teams fixing issues that do not materially affect risk.
Simbian’s approach focuses on risk in context, which dramatically improves prioritization and operational efficiency.
Another key distinction is operational responsibility.
Foundation model vendors typically ship tools that customers must operate themselves. These tools require security engineering expertise, DevOps resources, continuous tuning, and maintenance when models or APIs change.
This DIY model often places additional burden on already stretched security teams.
Simbian instead delivers turn-key platform, which includes continuous penetration testing and continuous monitoring, where the system continuously analyzes the entire environment using the AI Pentest Agent, proactively searches for threats using the AI Threat Hunt Agent, triages incoming alerts using the AI SOC Agent while recording agentic learnings and continuously improving based on human operator tribal knowledge feedback, and surfaces key findings across the organization, keeping stakeholders informed at multiple levels from operators to the CISO.
This model aligns with how many organizations prefer to run security programs, automation combined with operational reliability rather than experimental tooling that requires constant engineering effort.
Security findings only become valuable when they are tracked, assigned, and resolved.
Simbian integrates directly with existing operational workflows, for example Jira, email, Slack, Microsoft Teams, and enterprise case management systems. Every vulnerability or finding is prioritized, tracked as a case, assigned to the appropriate owner, and can be updated through natural language interactions with guardrails and approval flows.
In contrast, most AppSec tools stop at detection, leaving organizations to build the surrounding operational infrastructure themselves.
Model providers such as OpenAI and Anthropic have seen enormous volumes of code and training data. This gives them powerful capabilities in code analysis and generation.
However, operational security environments are fundamentally different from code repositories.
Real-world SecOps requires making decisions with incomplete data while dealing with legacy infrastructure, misconfigured systems, and mandatory integration into human workflows.
Simbian is built and tuned specifically for this messy production reality, using operational data that reflects how security teams actually work.
The result is tooling designed for live security environments, not idealized code analysis scenarios.
There is also a structural difference in business incentives.
Foundation model companies generate revenue primarily through token consumption. The more model usage occurs, the better their economics.
Simbian’s incentives are different.
The platform is designed to maximize security teams' operational efficiency, helping organizations avoid unnecessary remediation work, focus resources on the highest-impact risks, and automate large portions of security operations. Why continuously waste tokens fixing an application not ready for production instead of securing it using firewall rules until deployment?
In other words, the system aims to reduce waste, not increase computational consumption.
This alignment places Simbian directly on the customer’s side of the efficiency equation.
AppSec efforts by OpenAI and Anthropic provide real value, but they are marginal compared to the value Simbian AI delivers to security teams.
Layer | OpenAI / Anthropic | Simbian AI |
Core focus | Foundation models | AI-native SecOps platform |
Security scope | Application security tools | Full operational security |
Target users | Developers | Security teams, MSSPs, CISOs |
Operational model | DIY tooling | Turn-key continuous monitoring |
Context awareness | Code-level | Organization-wide Context Lake |
Workflow integration | Limited | Full case management and automation |
AI will play an increasing role across all areas of cybersecurity, including code security, infrastructure monitoring, and threat response.
Foundation model companies will likely continue expanding their AppSec tooling.
At the same time, platforms like Simbian is addressing a different challenge: bringing AI directly into the operational fabric of security teams.
By combining environmental context, continuous penetration testing, proactive threat hunting, learnings from daily SOC operations of alert triage, workflow automation, and other real-world SecOps data, the platform focuses on practical security outcomes rather than isolated vulnerability detection.
As organizations continue to scale their infrastructure and applications, this operational layer will become increasingly important.
And that is where AI-native SecOps platforms are positioned to make the largest impact.