Security analysts are burning out at an unprecedented rate. With 71% of SOC professionals reporting symptoms of burnout and 64% actively seeking new employment, the cybersecurity industry faces a crisis that threatens organizational security posture.
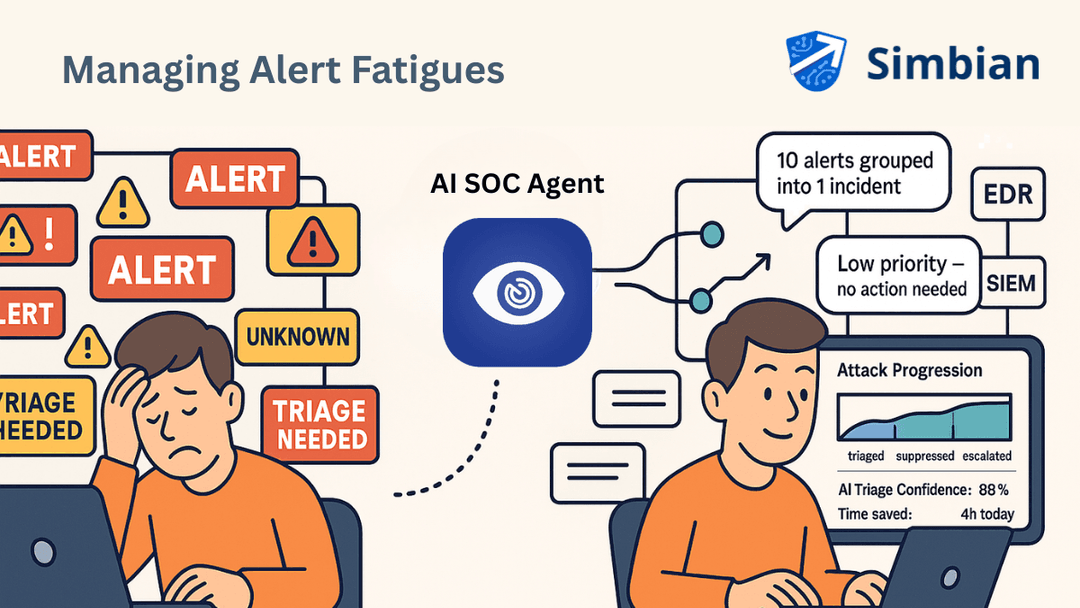
The root cause? Overwhelming amount of security alerts that changes skilled analysts into glorified alert processors, suffocating their expertise under an avalanche of false positives and repetitive tasks.
But a revolution is underway. AI SOC isn't just changing how we handle alerts; it's fundamentally transforming what it means to be a security analyst. Organizations implementing intelligent automation report not only improved security outcomes but also dramatically enhanced analyst satisfaction and productivity.
The numbers paint a stark picture of the modern SOC analyst's daily reality. The average security team processes over 3,800 alerts daily, with studies showing that approximately 52% of these alerts are false positives. This means analysts spend the majority of their time investigating non-threats, leaving little bandwidth for proactive security measures.
The psychological impact is severe. Alert fatigue doesn't just reduce productivity—it impairs decision-making capabilities. Analysts experiencing chronic alert overload show decreased accuracy in threat identification and slower response times to genuine incidents. This creates a dangerous cycle where increased alert volume leads to reduced effectiveness, potentially allowing real threats to slip through undetected.
Traditional SOC workflows compound this problem. Manual triage processes require analysts to context-switch constantly between different tools and interfaces, fragmenting their attention and reducing deep analytical thinking. The result? Talented professionals feel more like digital janitors than strategic security experts.
AI SOC automation represents a shift from reactive alert processing to proactive threat hunting. An AI SOC Agent exemplifies this transformation by autonomously handling routine investigative tasks while preserving human oversight for strategic decision-making.
The technology works by applying machine learning algorithms to alert triage, automatically filtering out false positives and enriching genuine threats with contextual information. This approach reduces analyst workload by up to 85% while improving threat detection accuracy.
- Intelligent Alert Prioritization and Filtering: AI systems excel at pattern recognition, automatically identifying and suppressing known false positives while escalating genuine threats. This intelligent filtering means analysts receive pre-qualified alerts with sufficient context to make immediate decisions about threat severity and response requirements. Organizations report that AI-powered alert filtering reduces noise by 90%, allowing analysts to focus on the 10% of alerts that represent genuine security concerns. This dramatic reduction in alert volume transforms the analyst's experience from overwhelming to manageable.
- Automated Evidence Collection and Correlation: Rather than manually gathering data from multiple sources, AI agents automatically collect and correlate relevant information from across the security stack. This includes network traffic analysis, endpoint data, user behavior patterns, and threat intelligence feeds. The result? Analysts receive comprehensive threat briefings rather than raw alerts, enabling faster decision-making and more effective response strategies. What once required hours of manual investigation now happens in minutes through automated data correlation.
- Contextual Threat Intelligence Integration: AI SOC systems automatically enrich alerts with relevant threat intelligence, providing analysts with immediate context about attack patterns, threat actor profiles, and recommended countermeasures. This contextual awareness dramatically improves response quality and reduces time-to-resolution. Analysts report that having immediate access to contextualized threat intelligence feels like having a senior expert constantly available for consultation, enhancing their confidence and decision-making capabilities.
- Predictive Analysis and Proactive Threat Hunting: Advanced AI systems don't just react to alerts—they proactively identify potential threats before they trigger traditional detection mechanisms. By analyzing behavioral patterns and identifying anomalies, AI enables analysts to transition from reactive to proactive security postures. This shift allows experienced analysts to focus on strategic threat hunting rather than alert triage, significantly increasing job satisfaction and professional development opportunities.
- Automated Incident Documentation and Reporting: AI systems automatically generate comprehensive incident reports, complete with timelines, evidence chains, and recommended remediation steps. This automation eliminates one of the most time-consuming aspects of incident response while ensuring consistent documentation standards. Security teams report that automated reporting saves 4-6 hours per incident while improving compliance and audit outcomes. Analysts can focus on analysis rather than administrative tasks.
- Continuous Learning and Adaptation: Unlike static rule-based systems, AI SOC platforms continuously learn from analyst feedback and emerging threats. This adaptive capability means the system becomes more effective over time, requiring less manual tuning and maintenance. Analysts appreciate working with systems that evolve alongside their expertise, creating a collaborative rather than adversarial relationship with automation technology.
- Enhanced Cross-Platform Integration and Workflow Automation: AI SOC systems integrate seamlessly with existing security infrastructure, automating workflows across multiple platforms and tools. This integration eliminates the context-switching that plagues traditional SOC operations, allowing analysts to work within unified interfaces.
The result is dramatically improved operational efficiency and reduced cognitive load, enabling analysts to maintain focus on high-value analytical tasks.
AI SOC automation doesn't replace human analysts—it elevates them. Organizations implementing intelligent automation report that analysts transition from alert processors to strategic security advisors, focusing on threat hunting, security architecture, and risk analysis.
This role evolution addresses the professional dissatisfaction that drives high turnover rates in traditional SOCs. Analysts report increased job satisfaction when they can apply their expertise to complex problems rather than repetitive tasks.
For security leaders facing the dual challenges of alert fatigue and analyst burnout, AI SOC automation offers a clear path forward. By automating routine tasks and enhancing human capabilities, organizations can transform their security operations from reactive firefighting to proactive threat prevention, creating work environments where skilled analysts can thrive while protecting organizational assets more effectively than ever before.
Implement AI in your SOC today!